Virus type: program stealing credit-card information.
Affected OS: Windows NT+, ATM software
Several modifications of the program with different functionality have been discovered.
Earlier versions disguise themselves as IsAdmin utility included in Windows Admin Script Tools. The malicious program displays messages typically displayed by the utility.
If the current user doesn’t have privileges to run the program it replaces C:\Program Files\Diebold\AgilisXFS\bin\SpiService.exe with its own file. The original file is saved as C:\Program Files\Diebold\AgilisXFS\bin\back.exe. In order to be launched as a system service Trojan.Skimer restores and restarts the service as soon as the installation is completed.
The main portion of malicious code is placed in the %windir%\lsass.exe created to run as the ProtectedStorage service. Two processes with the name lsass.exe exist in a compromised system. Only one of the processes is a genuine system process.
Information about all transactions conducted by the program as well as all intercepted keys is stored in %windir%\trl2 and %windir%\kl files.
Later versions of Trojan.Skimer consist of two components — the installer and dynamic library that integrates into ATM software. The installer is capable of updating the malicious program. It deletes the old version of %windir%\lsass.exe from the memory and hard drive and places all collected information into new files. Data from %windir%\trl2 is copied to %windir%\greenstone.bmp:redstone.bmp and information from %windir%\kl is placed into %windir%\greenstone.bmp:bluestone.bmp . If the file system is not NTFS, %windir%\redstone.bmp and %windir%\bluestone.bmp are used to store information.
After that the dynamic library of the Trojan is injected into the LogWriter process. To avoid an unnecessary installation the program checks if the running process has already been infected. If the process uses the system standard entry point, the code for loading of the malicious dll file is injected into the process. After that the process is stopped and the modified module is written onto the disk. Finally the malicious library is stored in the file thread of the service as pwrstr.dll.
The final step is injection of malicious code into the explorer.exe process. It uses the
"%windir%\Prefetch\
When the installation is completed, the malicious library and LogWriter process come into action. To maintain its operation the library injects its functions in all other processes of the ATM operating system
Running Trojan.Skimer requests current ATM status once in a second.
If a new inserted card is detected, an identification procedure is performed. The Trojan recognizes three types of cards
1. Ordinary card of a customer
2. Supervisor card
3. Limited functionality card
An ordinary card is a credit or debit card of a customer willing to use an ATM. If such a card is detected, the Trojan will only save information from the card.
A supervisor card is used to activate the menu of Trojan.Skimer. Functions provided by the menu will be described below.
A limited functionality card can be used to perform only one of the nine functions provided by a supervisor card.
A special card number generation procedure is used to identify supervisor or limited functionality cards. Trojan.Skimer recognizes checksums for cards of both types. Calculation of a check-sum is a combination of simple procedures with nine digits of the card number and digits related to additional bank information. This method is also used to define the number of of a limited functionality card. The function number is equal to the value specifying the month of the card expiration date.
If Trojan.Skimer detects that account balance information is received (sometimes it doesn’t happen), the Trojan will save theinformation as well. It recognizes three currency types – USD (U.S. dollars), RUR (Russian ruble) and UAH (Ukrainian grivna). If the currency is recognized, it will converted to USD at the following rate: 1 USD equals 26 RUR or 5 UAH
If the supervisor card is detected, the dialogue is displayed.
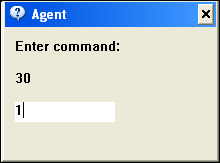
If no actions are performed in 30 seconds, the window will close.
A list of supported commands:
0. Exit
1. Uninstall. If the command is selected , all collected information and the program are removed from the system. The original LogWriter service file is restored.
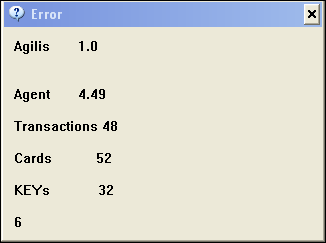
2. Display the ATM software version, the version of the Trojan and Trojan statistics.
3. Delete collected information
4. Reboot the terminal
5. If the command is selected, the program will wait for a special card with a chip to be inserted to download a new version of the library. If the download is successful, the old version of the library on the hard drive is replaced with a new one.
6. Print collected information.
7. A submenu. If the item is selected, the program will generate a number and one will have to enter a correct reply number.
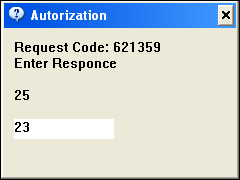
If a correct number is entered, a submenu will be opened
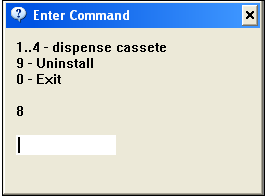
Entering numbers from 1 to 4 will send the ATM a command to dispense a corresponding cassette. If 9 is selected, the malicious library will be deleted but the collected information will remain intact.
8. Open the ATM service menu. The program opens the service menu of the ATM and automatically selects an item used ti display the internal counters of the ATM.
9. Performs the same function as. 6 but the data is written on the card with a chip.
The last known version of the program is 5.01 meaning that it has been in the wild for quite a while and that its authors continue its development.
