SHA1:
- f23c4e3dd93bc54ec67dc97023c0b1251a6ca784
Linux Trojan is designed to set up a SOCKS5 proxy server on the infected computer on the basis of the freeware source codes of the Satanic Socks Server.
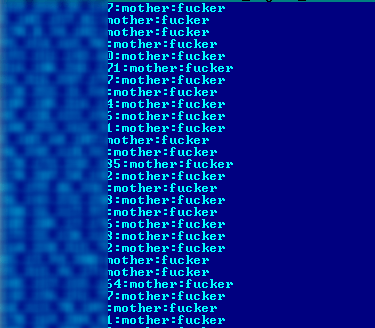
To distribute the Trojan, cybercriminals log in to the vulnerable devices via the SSH protocol. The list of vulnerable devices, as well as the logins and passwords that go with them, are stored on the server belonging to the cybercriminals. The lists look like this:
IP address:login:password
An example of such list can be seen in the following picture:
It is notable that users with such account details are usually created by other Linux Trojans. A script is generated with the help of this list, and it runs on the attacked devices using sshpass.
Port for access to proxy server is saved in the Trojan’s body during its compilation. Examined samples use the following ports:
18902
27891
28910
33922
37912
39012
48944
49082
49098
56494
61092
61301