sha1: ab8809c283ca6b950c0caf8a3cc69e8d270a1565
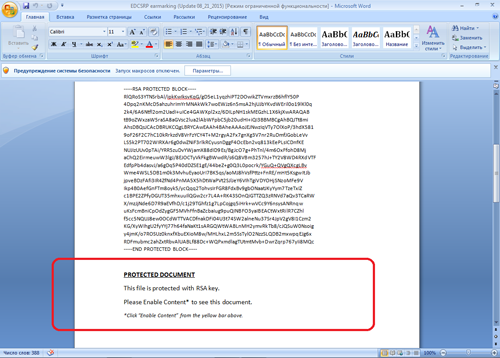
A downloader Trojan distributed as a Microsoft Word document in attachments to email messages. The document itself is supposed to be encrypted with RSA. To be able to read the contents of the message, the victim is prompted to enable macros.
The document also contains an empty page that actually has the text typed in white which becomes visible once the user enables macros. At the same time, the Trojan starts downloading several code fragments from the remote server. Using these fragments and depending on the Windows version, the malicious program generates scripts with .bat and .vbs extensions (for Microsoft Windows XP) or with a .ps1 extension (for Windows 7). The malware saves them on the computer and then runs. The scripts, in turn, download from the server controlled by cybercriminals another executable file and launch it.